An Unbiased View of Protection Against Ransomware
Wiki Article
Some Ideas on Rto You Should Know
Table of ContentsHow Ec2 Backup can Save You Time, Stress, and Money.Some Ideas on Data Protection You Need To KnowSome Known Details About Data Protection 9 Simple Techniques For Protection Against Ransomware
Data defense is the process of protecting important information from corruption, compromise or loss and giving the capacity to restore the information to a practical state ought to something happen to make the data inaccessible or unusable. Data security ensures that data is not damaged, is obtainable for licensed objectives only, and also is in conformity with appropriate lawful or governing requirements (aws backup).Figure: The Three Classifications of Information Defense The concept of data protection is to deploy methodologies and modern technologies to shield and make data available under all circumstances. Storage technologies can be used to secure information by utilizing disk, tape or cloud backup to safely keep copies of the information that can be used in the occasion of data loss or disruption.
g. cloning, matching, replication, snapshots, changed block monitoring, and so on,) are offering one more layer of data defense in enhancement to typical back-up. Modern technology advancements suggest that it is currently typical practice to give continual data defense which backs up the data whenever an adjustment is made to ensure that recuperation can be near-instantaneous.
These backups can change on-site disk and tape collections, or they can work as added safeguarded copies of data to provide a calamity recovery center. The data storage space industry checks out information defense generally from a technology point of view in what is required to keep information protect and readily available. Data defense is defined by the European Union (EU) in a very various way and is frequently used where various other areas may utilize the term information privacy.
How S3 Backup can Save You Time, Stress, and Money.
Information is at the center of company. Data is necessary to satisfying client requirements, responding to sudden market shifts and also unexpected occasions. Information security is the procedure of safeguarding digital information while keeping data usable for company objectives without trading client or end-user privacy.Today, it includes Io, T tools and sensors, commercial makers, robotics, wearables and also more. Data protection aids lower danger as well as allows a service or agency to react swiftly to threats. Data defense is very important since the complete number of computer devices boosts every year, and computer is now more complicated.
2 ZB of information was developed or duplicated. Not all data developed in 2020 was stored, however IDC suggests there is adequate proof storing extra data could benefit business.
The Best Strategy To Use For Aws Backup
The production field has a tendency to invest less resources in safeguarding industrial procedures innovation (OT) than in their enterprise networks. That leaves OT systems available to endanger. These OT systems consist of self-driving cars, robotics, Industrial Io, T devices and also sensors. Crucial infrastructure relies upon industrial control systems as well as a whole lot of various OT systems to function.The production industry is a prominent attack target, as well. In 2020, manufacturing, energy as well as healthcare fields dealt with the greatest price of strike according to IBMs Yearly X-Force Threat Index. Protecting business networks without providing the same attention to OT as well as devices opens them for an assault. Digital possessions are lucrative targets, even extra so as even more organizations function via digital growth initiatives connecting much more services.
Data safety and security for supply chains and also third-party access to systems is essential to shield them from cyberattacks. Balancing compliance with conference service goals can be a challenge if you do not have an information security approach in place.
The order focuses on activities to reinforce cybersecurity with bringing home critical infrastructure and federal government networks up to contemporary requirements. This will just obtain more facility as the government passes brand-new legislations and more carefully imposes older policies - https://sitereport.netcraft.com/?url=https://clumio.com.
The 9-Minute Rule for Data Protection
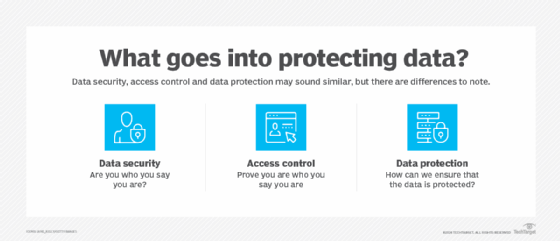
There remain no sweeping government legislations on consumer information privacy protections. Information security and data protection are comparable yet unique.A thorough information safety technique protects electronic possessions versus attack while representing and also protecting against expert threats. (These continue to be a leading source of information violations annually.) Releasing data safety and security devices and technologies give organizations a method to assess important data at its storage space locations. They also aid gain understanding right into just how people as well as devices are using it.
Report this wiki page